Microsemi Corporation, a provider of semiconductor solutions differentiated by power, security, reliability and performance, today announced the availability of its Secured Production Programming Solution (SPPS) for its field programmable gate arrays (FPGAs). The new solution securely generates and injects cryptographic keys and configuration bitstreams into Microsemi’s FPGAs thus preventing cloning, reverse engineering, malware insertion, leakage of sensitive intellectual property (IP) such as trade secrets or classified data, overbuilding and other securitythreats.
Microsemi Corporation, a provider of semiconductor solutions differentiated by power, security, reliability and performance, today announced the availability of its Secured Production Programming Solution (SPPS) for its field programmable gate arrays (FPGAs). The new solution securely generates and injects cryptographic keys and configuration bitstreams into Microsemi’s FPGAs thus preventing cloning, reverse engineering, malware insertion, leakage of sensitive intellectual property (IP) such as trade secrets or classified data, overbuilding and other securitythreats.
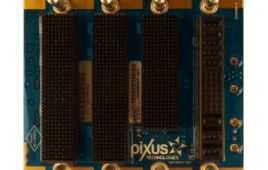
Microsemi’s SPPS includes the use of “customer” and “manufacturer” hardware security modules (HSMs) combined with Microsemi firmware, the company’s new SPPS Job Manager software and state-of-the-art security protocols built into every Microsemi SmartFusion™2 system-on-chip (SoC) FPGA and IGLOO™2 FPGA. SPPS allows customers to automatically prevent today’s major security threats by external adversaries or competitors, contract manufacturers and their employees, or other insiders. SPPS is an ideal solution for any FPGA-based system that may be at risk for overbuilding in a wide variety of applications in the communications, defense, industrial and automotive markets.
Protecting IP and Revenue
The U.S. Chamber of Commerce estimates that IP threats cost domestic companies more than $250 billion per year in lost revenues, as well as the loss of approximately 750,000 jobs. More than 55 million jobs in the U.S. are supported by IP-intensive industries.
Microsemi’s SPPS Job Manager software generates a job file containing encrypted security parameters, authorized production device limit counts and an FPGA bitstream, allowing the user to monitor all aspects of the FPGA production job, including specifying the key management options desired and allowing them to assert positive control over the number of systems produced. This file is only readable by the target manufacturing HSM. The SPPS also generates encrypted files for the reconfiguration of FPGAs previously “keyed” by the user, such as those in fielded systems.
All security-sensitive operations including device authentication (to provide supply chain assurance), cryptographic key generation, bitstream encryption, the authorization and counting of produced systems, and the signing of audit logs are performed within the hardware security boundary of the FIPS140-2 level 3 certifiedThales HSMs, rather than in a more vulnerable open Windows or Linux computer workstation. This provides the highest level of security in the FPGA industry for detecting counterfeit devices, protecting design IP and preventing overbuilding.
Microsemi
microsemi.com
The post FPGAs get cryptographic keys to prevent cloning appeared first on Microcontroller Tips.
Filed Under: Microcontroller Tips