Pinging is the process whereby we send an exploratory probe or packet consisting of 64 bytes or more to a network node. It contains a return request and takes its name from the analogous pulse of sound sent and received by a sonar installation. When this burst of data is returned, certain information becomes available including errors and packet loss, and this is valuable for troubleshooting, educational and developmental purposes. First we’ll see how it is done, and then discuss some implications.
The procedure varies depending upon your platform and operating system, but it is always quite simple and executes quickly. It can be done as a command-line procedure, but we’ll look at a simpler implementation. As an example, we’ll do it in Mac OS X. For other machines, go here. Exact details may differ, but here is the basic idea:
1) Quit all irrelevant programs such as any browsers or word processing applications so that only the Finder remains active.
2) In the Menu bar, click on Go, then from the drop-down menu click on Utilities.
3) In the window that opens, click on Network Utility.
4) At the top of the window that appears, click on Ping.
That’s all there is to it. In the Ping window, fill in the information and click on Ping. Notice that for the network node to be pinged, either the Universal Resource Locator (URL) or the Internet Protocol (IP) address may be used.
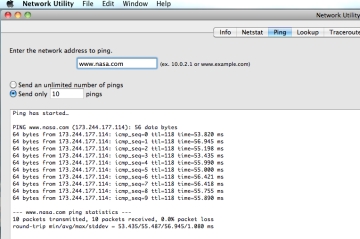
Nasa.com comes in around 55 msec.
Ping some network nodes, just to see how it works. Google is a good candidate. The stipulated number (or a continuous stream) of pings is sent. Google has competent developers whose efforts at making a fast opening page have resulted in a quick round trip averaging about 43 msec. Yahoo runs about 10 msec slower. Checking some IP addresses at random, I found that many run around 95 msec.
Besides speed, other information such as whois and traceroute is available from the tabs along the top of the window. Perhaps the single most valuable result is presence or absence of a response.
Many implementations include an option called “flood ping,” which is a successor to the easily countered “ping of death.” This procedure consists of sending ping requests at an extremely fast rate so the response time can be ascertained under high-load conditions.
Flood ping has been used as a malevolent tool in denial-of-service attacks. For that reason, its use is restricted to those with administrative privileges, although an evil genius will eventually work around such measures.
The post Sizing up networks with pinging appeared first on Test & Measurement Tips.
Filed Under: Test & Measurement Tips