Tips and techniques that will help you set up and maintain an industrial Ethernet network.
Industrial Ethernet is used to connect devices such as PLCs, local and distributed I/O, servo controllers and drives on the plant floor and in industrial facilities. In this capacity, it links many pieces of hardware—and has many cables, connections and configurations options.
For visualization and monitoring, industrial Ethernet connects PC-based and embedded HMIs to controllers, and to each other. It’s also used to connect HMIs to the Internet, and to upper level servers running historian, quality, manufacturing and other enterprise applications.
All of these industrial Ethernet communications require two things: a physical connection or layer, and configuration based on the protocol. The physical connection defines the electrical, cable and connection requirements. The protocol configuration specifies the common language of the data in the communication messages.

Switches are an important part of any Ethernet installation, and managed switches can often significantly improve performance of the network.(Source: AutomationDirect.com)
Start with the basics
Industrial Ethernet cables are not created equal, so consider network speeds when designing and selecting cabling. Then, select the communication protocol to communicate between devices.
Once you have determined protocols and network speed needs, you will face a choice of selecting a patch cable or crossover cable, and does it matter? In the commercial world, most devices can auto crossover (Auto-MDIX) and use crossover cabling, but not all industrial devices can. Thus, the recommendation is to use patch cables for connecting end devices such as PLCs and HMIs to Ethernet switches, and use crossover cables to connect end devices together directly without a switch.
RJ-45 connectors are used for most Ethernet connections, but many devices use this same connector for RS-232. Carefully check the technical data of the device before plugging it in.
With the connection understood, the question of shielded versus un-shielded often comes up in industrial Ethernet applications. It’s good design practice to use shielded cable when possible in industrial environments because electrical noise is often present from motors, VFDs, welding and so on. It’s also good practice to use at least Cat5e, but Cat6 cable is the better way to go, especially for the higher gigabit speeds. The choice of cabling should be specified based on run distance, bandwidth and other requirements.
Another requirement to consider for both performance and compatibility is communication speed, and half or full duplex capability. While duplex compatibility can be overcome by using a managed switch—discussed in more detail later—performance is limited to the slowest device.
For most industrial automation applications, the link speed is often 100 Mb, and it’s not critical since most industrial protocols don’t require anywhere near the full speed (bandwidth) available. However, the link speed is an additive factor when looking at performance.
With half duplex devices, the device (node) can only transmit or receive data; it can’t do both simultaneously. Thus, its performance is slower than full duplex arrangements, which can do both. Plus, it is common to see half duplex devices drop packets under heavy load due to data collisions.
Most devices (nodes) with a bandwidth of 100 Mb or more use full duplex. While this speeds data transmission, there can still be compatibility issues.
Even though Device A has an Ethernet port and Device B has an Ethernet port, they may not be able to communicate with each other. Chances are, the devices are using more layers for communication than just Ethernet. They are probably using multiple layers based on the Open System Interconnection (OSI) model, which defines seven layers (Figure 1) for communication. Each layer used should be understood by both devices.

The Open Systems Interconnection model is a common reference model showing how applications can communicate over a network.
With most operating systems, the lower OSI layers of physical medium data link with MAC address, network with IP address, and transport with TCP or UDP, and will be understood by both devices. More research is often needed to understand if some of the uppermost layers—such as the session, presentation and applications layers—are common to both devices.
Some examples of application layer protocols in industry are Modbus TCP, Ethernet/IP and Profinet. However, even with compatible layers, both networked devices must support protocol functions.
Unmanaged versus managed switches
Industrial ethernet network topologies include the bus, ring and star. Bus and ring are similar to a daisy-chain connection where a single cable hops between each device. Bus topology is a bit obsolete, while the newer ring topology adds fault tolerance. However, most industrial Ethernet installations use star topology, with some ring connections to reduce cable run distances.
With the star topology, a switch connects devices to a central access point. Ethernet switches come in both unmanaged and managed configurations. There are applications and situations that make sense for unmanaged switches, and there are others where a managed switch is a far better choice.
When connecting a device to a switch, it automatically negotiates to an agreed upon speed and duplex mode. Auto negotiation can be tricky and will often fail. It is better to turn off auto negotiation, using a managed switch, and fix the speed and duplex to a known working setting for both sides. This can be particularly helpful when connecting together devices from different manufacturers.
For a simple network with five or fewer devices in a relatively small area, an unmanaged switch will usually work, and it will always be less expensive than its managed equivalent.
For larger applications with many devices from several manufacturers, consider a managed switch. Often these applications include extensive multicasting, using Ethernet/IP for example, and are spread out over a large area. A managed switch’s configuration and problem solving features will easily outweigh the cost premium over an unmanaged switch in most complex applications.
IP addresses and MAC addresses are targeted at specific devices. But there are two other types of messages that are targeted at multiple devices: broadcasts and multicasts. It takes a router to stop broadcast messages, but managed switches can intelligently route multicast messages to the correct ports by using IGMP snooping. The switch will learn which ports should be receiving multicast messages (by “IGMP Join” messages) and only send messages to those ports, enhancing system performance.
Managed switches can filter out multicast messages used in Ethernet/IP. Managed switches can also prevent the network from shutting down if someone accidently loops the switches.
If unmanaged switches are mistakenly connected together in a ring, a broadcast storm will occur and shut down the network. Managed switches prevent this by shutting down one path of the ring. If something happens to the working path, the switch changes over to the other path, which also provides a level of redundancy.
Subnetting and networking
The media access control (MAC) address is the “hard” physical address of a device. The address is set during manufacturing and should never change. Although there are exceptions to this, hard coding the MAC address was the original intent of the design. An Ethernet packet cannot enter a device without this address. However, it’s rare that a communication setup or configuration will need this address because another protocol, called address resolution protocol (ARP), usually automatically retrieves it and correlates it to an IP address.
The IP address is the logical address of a device, used to identify an address and network of the specific device. An IP address, such as 192.168.070.001, includes two identifiers: the network address and the host address. The network address helps devices and routers determine where to send messages. The host address identifies the specific device on that network. The subnet mask, such as 255.255.255.000, determines which part of an IP address is the network address and which part is the host address.
The subnet mask determines the portion of the IP address that is network and host. Wherever there are 1s in the mask, the corresponding bit location of the IP address is part of the network address. Wherever there are 0s in the mask, the corresponding bit location of the IP address is part of the host address.
The default gateway address and a router enable connections to other networks. A device can only send and receive Ethernet messages to other devices on its network as determined by the IP address and subnet mask. If a device needs to communicate with a device on another network, a router is required. To get the message to the other network, the device will send its message to the default gateway address, which is the IP address of the router.
Local area network (LAN) and wide area network (WAN) definitions vary greatly, but in general LANs are networks encompassing switches and hubs. Once a network traverses across a router, these networks are encompassed within a WAN.
Subnet specifics
As noted above, IP addresses in conjunction with subnet masks logically separate networks into subnets that typically do the same kind of work. Subnets are separated by routers, and messages can traverse across these routers through the default gateway address (router address). If two devices are on the same LAN and need to communicate to each other, their subnets must be compatible and their host addresses unique. If not, they cannot communicate to each other without the help of a router.
To determine whether two devices can communicate to each other on a LAN without a router, apply the subnet mask of each device to its respective IP address to see if the resulting network addresses are the same. If they are, they should be able to communicate. This calculation can be done manually, but there are many website and mobile applications to assist.
For example, at www.subnet-calculator.com, one can simply enter the IP address and subnet mask, and it will calculate the range of possible devices that can communicate to each other. Another concept called network class is included with this tool. The network class is determined by whether there are many subnets with relatively few devices (hosts) or fewer networks with many hosts, such as the Internet. For most private networks inside of a company, Class B or Class C will be the network class of choice.
Remote access—routers and firewalls
Remote access speeds are increasing, reducing the need to be on-site for many monitoring, adjustment and troubleshooting activities. However, accessing devices behind a router and firewall adds some complexities to how devices connect at a remote facility.
NAT stands for Network Address Translation. The purpose of NAT is to allow a facility to give many devices access to the Internet without requiring a public IP address for each one as there is a cost associated with each required public IP address. The router/firewall will translate the IP addresses of outgoing and incoming messages to and from the Internet so that anyone outside of the company network will only see the public IP address.
Port Forwarding is a feature of a router/firewall allowing messages coming from the Internet to go to a specific device on the inside of that network. Outgoing messages get handled automatically. The router keeps track of where a message originated from within the network by means of the port number, and matches up the response to the original message. But a router does not know where to send an incoming message simply by means of the IP address as the device originating the message does not know the internal IP addresses of all the devices. The port number is used for this purpose.
The router has a configuration table that allows the user to determine the correct internal IP address by specifying the port number receiving the message. But Port Forwarding is not the most secure method of allowing remote access because opening up a port can open up a door for other devices to come in and cause trouble.
A VPN is a far more secure way to access devices remotely. A virtual private network (VPN) connects to a router/firewall with VPN server capability from a remote device that makes it look like they coexist on the same local network. A connection is established between the local and remote devices by means of a local VPN router, or through use of a VPN client software tool that runs on a PC or device. Once connected, the VPN server gives the remote device an IP address of the internal network, and the remote device can communicate to the devices on the internal network without routing.
There are different ways to configure and connect a VPN, and these connections can be more complex and difficult to setup initially. But once this initial effort is completed, VPNs provide easier and more secure remote connectivity.
Wireshark hunts down problems
Much diagnostic information is available in a managed switch. Here’s how to access and make sense of this information.
Port mirroring can be used to specify a port to send all of the messages from one or more devices. A PC running a free tool called Wireshark (www.wireshark.org) can be connected to this mirror port. Wireshark will grab and display all of the messages from those devices, which will show exactly what is occurring in the way of communications. This tool helps when connections and configurations are complete but problems still remain.
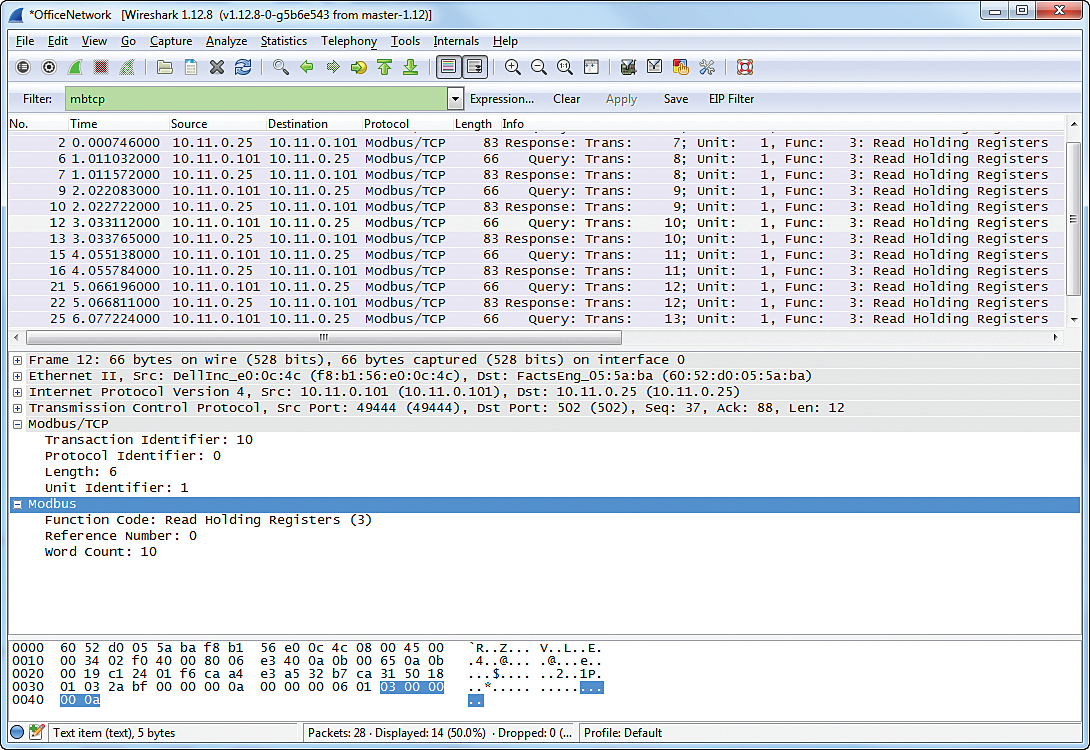
This Wireshark troubleshooting tool dashboard enables analysis of Ethernet data and detection of problems.
Wireshark is an invaluable tool, and you don’t have to be a protocol expert to use it to solve most Ethernet issues. For more complex problems, you can take captures of the data, save it to a file, and send it to others who are protocol experts. It can save you hours and hours of troubleshooting time.
AutomationDirect
www.automationdirect.com
by Chris Harris, Team Lead – Technology Assistance Group at AutomationDirect.com
Filed Under: Ethernet — cables • hubs • switches, CONNECTIVITY • fieldbuses • networks, Displays • HMIs • operator interfaces • monitors, PLCs + PACs






Tell Us What You Think!